Copyright © Fidelis Security. All rights reserved.
-
Privacy PolicyPrivacy Policy
-
Terms of ServiceTerms of Service
-
Trust CenterTrust Center
-
SecuritySecurity
Uncovering Critical Vulnerabilities and Malicious Tactics The Fidelis Security Threat...
Read Research Report
Stay informed on May 2023 cybersecurity incidents with Fidelis Security's...
Read Research Report
Explore the major cybersecurity threats of April 2023 including state-sponsored...
Read Research Report
Cyber-attacks on the Ukrainian government organizations and its critical infrastructure...
Read Research Report
Download the Threat Intelligence Report now to stay updated on...
Read Research Report
Stay Informed and Ahead Emerging Threats and Critical Events Fidelis...
Read Research Report
Uncover January 2023 Cyber Threats, Vulnerabilities, Exploits, and Security News.
Read Research Report
December 2022 TRT examines new vulnerabilities, mitigations for the ongoing...
Read Research Report
The Fidelis security Threat Intelligence Summary highlights the most critical...
Read Research Report
The Fidelis Security Threat Intelligence Summary highlights the most critical...
Read Research Report
The latest iterations of destructive malware that impacted Ukraine
Read Research Report
The Ukrainian region has suffered a string of cyber-attacks against...
Read Research ReportThe Fidelis Security Threat Intelligence Summary highlights the most critical emerging vulnerabilities and malware. The June 2023 report reveals ongoing instances of non-compliance with CISA Directives regarding MOVEit vulnerabilities, Russian state-sponsored threat actors leveraging PowerShell USB malware, and the emergence of Akira Ransomware targeting ESXi servers. Stay updated with our insights to get ahead of emerging threats and tactics used by malicious actors.
As part of the ongoing Russian offensive, the Ukrainian region has suffered a string of cyber-attacks against government agencies, the banking community, and defense industries.
These attacks on the Ukrainian government organizations and its critical infrastructure have far-reaching consequences both within and beyond the region. Through our continued vigilance, we’ve tracked these attacks to help our customers conduct proactive threat hunting related. This report details the most critical events we have tracked so far, providing a resource so than any organization can prepare for and respond to disruptive cyber activity.
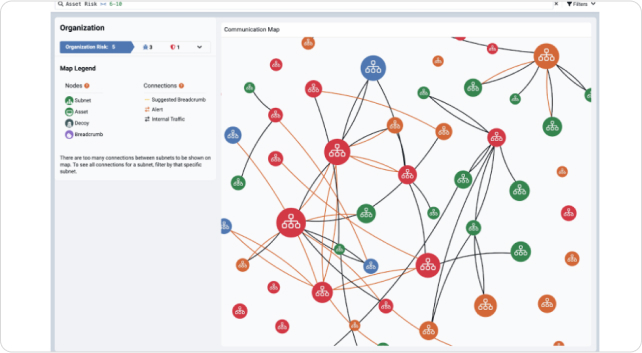
Active Directory (AD) is an attacker’s gold mine. It supplies centralized identity and group management for access to network resources which makes it the best place for an attacker.
Join our newsletter to stay up to date on features and releases.