Summary
CVE-2025-53786 is a serious flaw in Microsoft Exchange hybrid setups. It lets on-premises admins gain higher privileges in Exchange Online because of shared service principal settings. Exploitation could occur without leaving easily detectable audit traces.
Urgent Actions Required
- Install the April 2025 Hotfix[2] (or later) on all on-prem Exchange servers
- Switch to a dedicated Exchange hybrid app using the provided script or updated wizard.
- Run Service Principal Clean-Up to reset credentials and remove old trust.
- Check hybrid setup with Exchange Health Checker for any issues.
- Disconnect unsupported or old Exchange servers from the internet until secured.
Which Systems Are Vulnerable to CVE-2025-53786?
Technical Overview
- Vulnerability Type: Elevation of Privilege via Shared Service Principal in Hybrid Exchange Deployments (CWE-287: Improper Authentication)
-
Affected Software/Versions:
- Microsoft Exchange Server 2016 – Cumulative Update 23 (build 15.01.2507.055)
- Microsoft Exchange Server 2019 – Cumulative Update 14 (build 15.02.1544.025)
- Microsoft Exchange Server 2019 – Cumulative Update 15 (build 15.02.1748.024)
- Microsoft Exchange Server Subscription Edition – RTM (build 15.02.2562.017)
- Attack Vector: Network (requires administrative access to on-premises Exchange)
- CVSS Score: 8.0
-
CVSS Vector: CVSS: 3.1
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: High
- User Interaction: None
- Scope: Changed
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
-
Patch Availability: Yes, available.
Hotfix update for Exchange Server 2019 CU15: April 18, 2025 (KB5050672) - Microsoft Support
CVE-2025-53786 - Security Update Guide - Microsoft - Microsoft Exchange Server Hybrid Deployment Elevation of Privilege Vulnerability
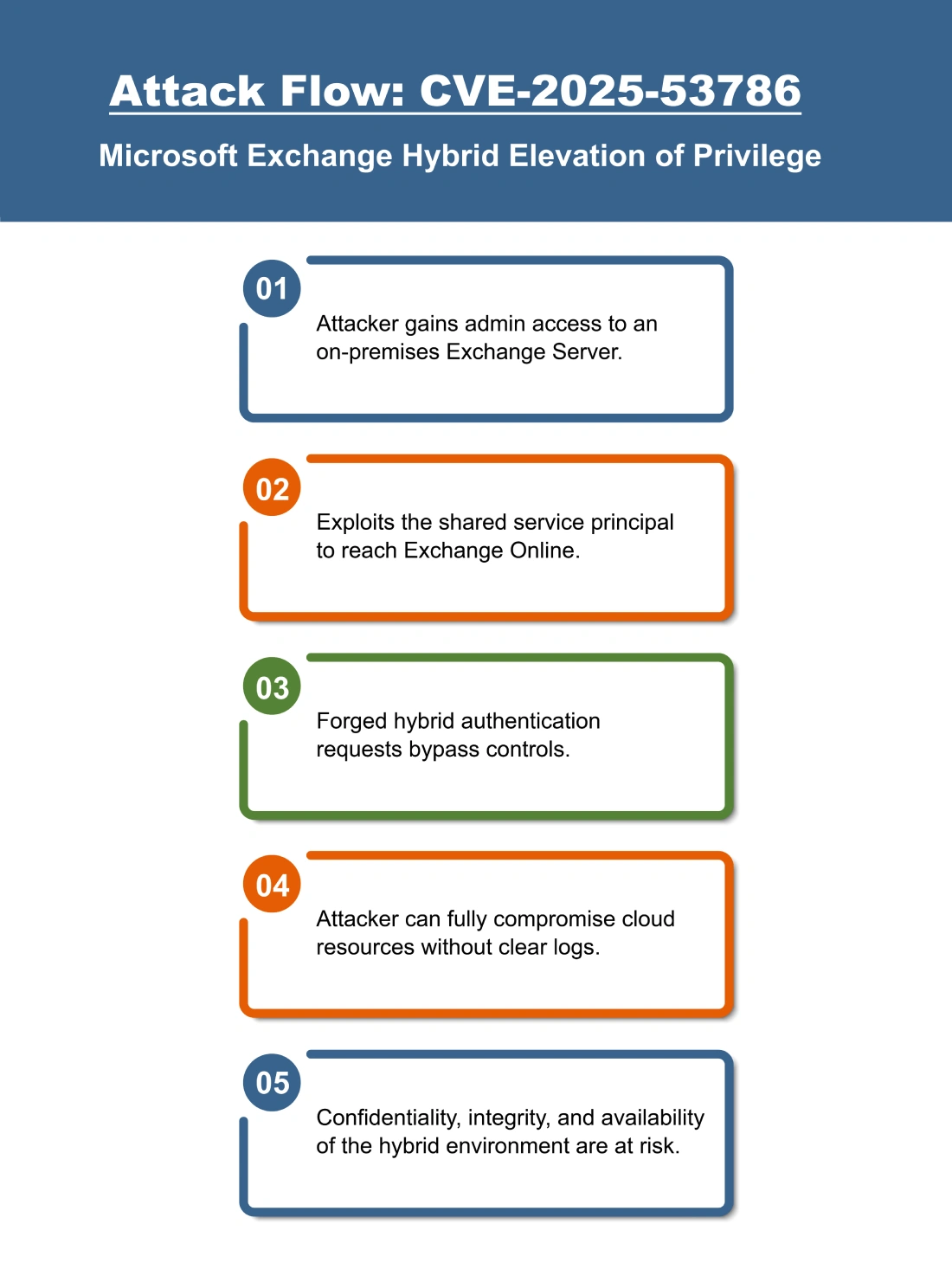
How Does the CVE-2025-53786 Exploit Work?
The attack typically follows these steps:
What Causes CVE-2025-53786?
Vulnerability Root Cause:
This vulnerability happens because Exchange hybrid uses a shared service principal. If the switch to a dedicated hybrid app isn’t fully done, admins on on-premises servers can impersonate hybrid requests and access Exchange Online without being detected.
How Can You Mitigate CVE-2025-53786?
If immediate patching is delayed or not possible:
- Ensure unsupported or end-of-life Exchange servers are disconnected from the internet.
- Temporarily restrict administrative access to on-premises Exchange servers.
- Review hybrid configuration and service principal credentials to detect any misconfigurations.
- Monitor for unusual administrative activity or changes in Exchange hybrid operations.
Which Assets and Systems Are at Risk?
Asset Types Affected:
- On-premises Exchange Servers – 2016 CU23, 2019 CU14/CU15, and Subscription Edition RTM.
- Hybrid Exchange configurations – Environments connecting on-premises Exchange with Exchange Online using shared service principals.
- Administrative accounts – Users with admin privileges on affected Exchange servers.
Business-Critical Systems at Risk:
- Exchange Online tenant – Compromise could allow attackers to escalate privileges and access cloud resources.
- Hybrid-enabled collaboration features – Free/Busy calendar lookups, MailTips, profile pictures, and other rich coexistence functionalities.
- Connected services – Potential impact on SharePoint Online and other linked Microsoft 365 services.
Exposure Level:
- Internet-facing Exchange servers – Particularly those with hybrid configuration and administrative access exposed.
- Internal environments – On-premises Exchange servers with privileged accounts remain vulnerable if not patched or reconfigured.
- Hybrid configurations not migrated to dedicated service principal – Attackers could exploit remaining trust relationships.
Will Patching CVE-2025-53786 Cause Downtime?
Patch application impact: Low. Apply April 2025 Hotfix (or later) and configure the dedicated hybrid app; minimal downtime.
Mitigation (if immediate patching is not possible): Disconnect unsupported servers from the internet and run Service Principal Clean-Up Mode to reset shared credentials.
How Can You Detect CVE-2025-53786 Exploitation?
Exploitation Signatures:
- Administrative access on on-premises Exchange servers followed by actions in the connected Exchange Online environment without expected audit logs.
- Use of hybrid features (Free/Busy, MailTips, profile sharing) without standard authentication flows.
MITRE ATT&CK Mapping:
Indicators of Compromise (IOCs/IOAs):
- Unauthorized changes or access in Exchange Online performed from on-prem Exchange admin accounts.
- Abnormal activity in hybrid application permissions or keyCredentials.
Behavioral Indicators:
- Access to cloud resources bypassing standard hybrid authentication checks.
- Missing expected audit events during privileged operations.
Alerting Strategy:
- Priority: Critical
-
Trigger alerts for:
- Trigger alerts for administrative operations in Exchange Online performed without corresponding hybrid authentication logs.
- Monitor for unexpected changes to dedicated hybrid app or keyCredentials.
Remediation & Response
Patch/Upgrade Instructions:
Mitigation Steps if No Patch:
- Disconnect unsupported or end-of-life Exchange servers from the internet.
- Monitor hybrid configurations and service principal keyCredentials for unusual changes.
- Limit administrative access to on-premises Exchange servers to trusted personnel only.
Compliance & Governance Notes
Audit Trail Requirement:
- Record that Hotfix and configuration steps were applied, including date, time, and target servers.
- Ensure the dedicated hybrid app is fully configured before October 2025.
Where Can I Find More Information on CVE-2025-53786?
- ^NVD – CVE-2025-53786
- ^Microsoft Releases Guidance on High-Severity Vulnerability (CVE-2025-53786) in Hybrid Exchange Deployments | CISA
- ^Released: April 2025 Exchange Server Hotfix Updates | Microsoft Community Hub
- ^CVE-2025-53786 – Security Update Guide – Microsoft – Microsoft Exchange Server Hybrid Deployment Elevation of Privilege Vulnerability
- ^Valid Accounts, Technique T1078 – Enterprise | MITRE ATT&CK®
- ^Exploit Public-Facing Application, Technique T1190 – Enterprise | MITRE ATT&CK®
CVSS Breakdown Table
| Metric | Value | Description |
|---|---|---|
| Base Score | 8.0 | High severity; allows privilege escalation from on-premises Exchange to Exchange Online. |
| Attack Vector | Network | Exploitable remotely over the network once attacker has on-premises admin access. |
| Attack Complexity | High | Exploitation depends on hybrid configuration and admin privileges. |
| Privileges Required | High | Attacker must already have administrator rights on an on-premises Exchange Server. |
| User Interaction | None | No additional user action is required. |
| Scope | Changed | Exploitation impacts connected Exchange Online environment. |
| Confidentiality Impact | High | Identity integrity of Exchange Online accounts could be compromised. |
| Integrity Impact | High | Attacker could gain administrative control in the cloud. |
| Availability Impact | High | Successful exploitation can disrupt cloud services and access to Exchange Online resources. |