Summary
CVE-2025-43300 is an out-of-bounds write (CWE-787) in Apple’s Image I/O / RawCamera image processing code. A crafted DNG/JPEG-lossless image can trigger a buffer overwrite when metadata (e.g., TIFF SamplesPerPixel) disagrees with the JPEG SOF3 component count. Unpatched systems processing such files may suffer memory corruption, crashes, and — in targeted real-world cases reported by Apple and researchers — potential arbitrary code execution. Apple has released fixes across iOS, iPadOS and macOS; CISA added this CVE to its Known Exploited Vulnerabilities list.
Urgent Actions Required
- Update iPhones and iPads to iOS/iPadOS 18.6.2.
- Update Macs to macOS Sequoia 15.6.1, Sonoma 14.7.8, or Ventura 13.7.8.
- Identify unpatched devices and apply updates immediately.
- Use MDM tools to enforce updates across all corporate devices.
Which Systems Are Vulnerable to CVE-2025-43300?
Technical Overview
- Vulnerability Type: Out-of-Bounds Write in Image Processing Framework
-
Affected Software/Versions:
- iOS / iPadOS 18.6.1 and earlier
- macOS Ventura (before 13.7.8)
- macOS Sonoma (before 14.7.8)
- macOS Sequoia (before 15.6.1)
- iPadOS (before 17.7.10)
- Attack Vector: Network (Exploitation possible through crafted image or DNG files delivered via iMessage, Mail, Safari, or similar applications).
- CVSS Score: 8.8
-
CVSS Vector: v3.1
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
- Patch Availability: Yes, available
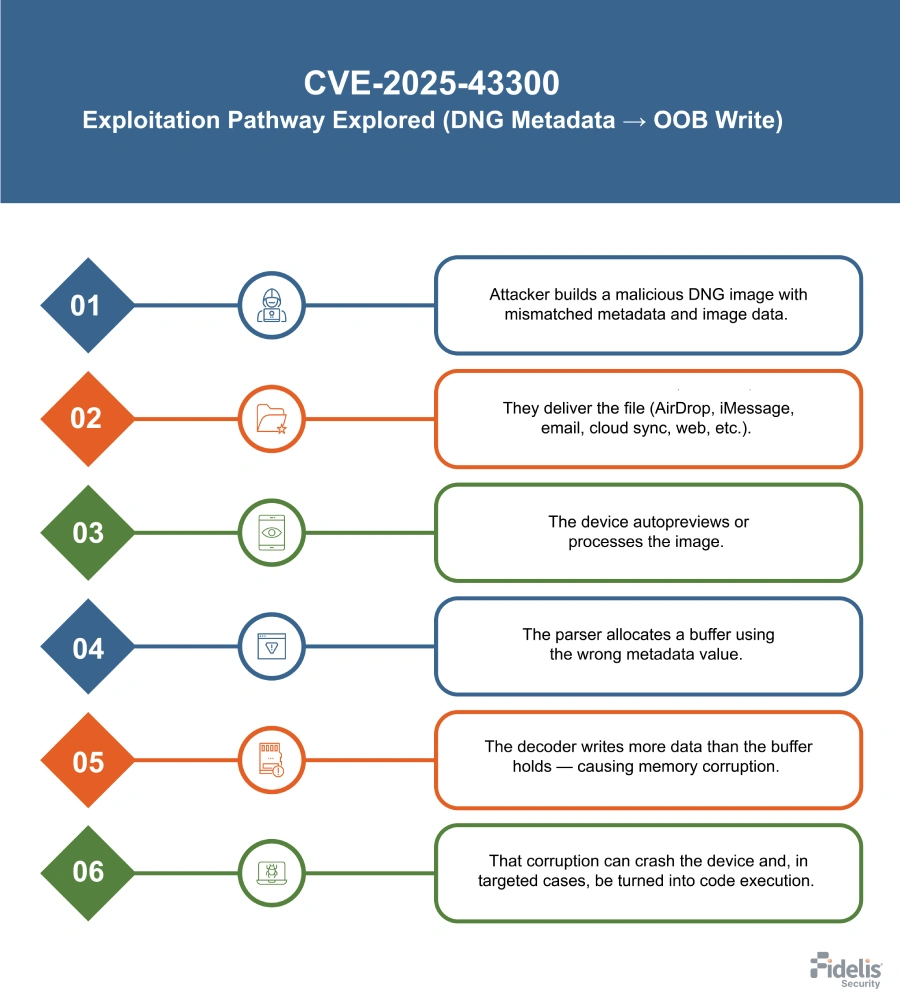
How Does the CVE-2025-43300 Exploit Work?
Here’s how the attack works:
What Causes CVE-2025-43300?
Vulnerability Root Cause:
The defect is a validation gap between DNG/TIFF metadata and the embedded JPEG Lossless stream in Apple’s image parsing code (RawCamera.bundle / Image I/O). The parser trusts the SamplesPerPixel metadata when allocating buffers, while the JPEG decoder later uses the SOF3 component count from the stream. When those values conflict, more pixel data is written than the buffer was sized for — an out‑of‑bounds write (CWE‑787) that leads to memory corruption.
How Can You Mitigate CVE-2025-43300?
If patching is delayed or not feasible:
- Do not open unsolicited or unknown image files (DNG/JPEG) on unpatched devices.
- Disable automatic image previews in mail, messaging, and filesync clients where possible.
- Block or restrict AirDrop and other adhoc file transfers for highrisk users.
- Put highvalue accounts into Apple Lockdown Mode (if operationally acceptable).
- Enforce stricter attachment handling: strip/scan image attachments before delivery to endpoints.
- Use MDM to limit automatic media processing and to enforce temporary configuration restrictions.
- Increase logging and monitor for imagerelated crashes or abnormal RawCamera/ImageIO activity.
- Ingest and apply community detection rules and tools published by researchers to spot exploitation attempts.
- Never run PoC or untrusted DNG files on production devices — analyze only in isolated labs/VMs.
- Prioritize patch deployment for high-risk devices and track remediation progress.
Which Assets and Systems Are at Risk?
Asset Types Affected:
- Endpoints: iPhones, iPads, and Mac computers running vulnerable OS versions.
- Applications: Any app that uses Apple’s Image I/O / RawCamera (e.g., Mail, Messages, Safari, photo preview/thumbnail services).
- Mobile devices in BYOD fleets: Personal devices that access corporate data or resources.
Business-Critical Systems at Risk:
- Highvalue user devices: Execs, journalists, researchers, privileged accounts — targets in reported campaigns.
- Corporate Macs and managed iOS/iPadOS devices: Devices that store or access sensitive business information.
- Photo-sync and mediaprocessing workflows: Services or endpoints that automatically ingest and preview image files.
Exposure Level:
- Wide exposure: Any device that receives or autopreviews image files (AirDrop, iMessage, email attachments, cloud sync, web downloads).
- High risk for unpatched devices: Targeted exploitation documented; unpatched endpoints are especially vulnerable.
- Not limited to publicfacing services: Risk arises through normal user interaction or automatic image processing, not only via externally exposed servers.
Will Patching CVE-2025-43300 Cause Downtime?
Patch application impact: Low. Updating to iOS / iPadOS 18.6.2, iPadOS 17.7.10, macOS Ventura 13.7.8, macOS Sonoma 14.7.8, or macOS Sequoia 15.6.1 resolves the vulnerability. Installation is straightforward, requires minimal user interaction, and causes only brief device restart downtime.
How Can You Detect CVE-2025-43300 Exploitation?
Exploitation Signatures:
- Presence of PoC repos/tools: b1n4r1b01/n-days, hunters-sec/CVE-2025-43300, h4xnz/CVE-2025-43300, dng_vulnerability_analyzer.py, hex_modifier.py, ELEGANT BOUNCER.
- DNG sample names used in research (e.g., IMGP0847.DNG).
- Files matching PoC binary diffs or generated vuln POCs (vuln_poc_IMGP0847.dng - style).
Indicators of Compromise (IOCs/IOAs):
- Devices running OS versions before the fixes (unpatched iOS/iPadOS/macOS).
- PoC files or repo clones found in user directories, downloads, or internal repos.
- Unexpected copies of dng_vulnerability_analyzer.py, hex_modifier.py, or ELEGANT BOUNCER.
Behavioral Indicators:
- Crashes in Image I/O / RawCamera.bundle.
- App crashes immediately after receiving or previewing an image.
- Repeated thumbnail/preview failures or memory-access faults tied to image handling.
Alerting Strategy:
- Priority: High
-
Trigger on:
- Detection of PoC files/repos on internal systems.
- Imagehandling crash on an unpatched or highvalue device after receiving a DNG/image.
- Unpatched highvalue user processed a DNG attachment.
- Alert should include: device ID, OS version, filename, timestamp, and crash log excerpt.
Where Can I Find More Information on CVE-2025-43300?
- ^About the security content of iOS 18.6.2 and iPadOS 18.6.2 – Apple Support
- ^About the security content of macOS Ventura 13.7.8 – Apple Support
- ^About the security content of macOS Sonoma 14.7.8 – Apple Support
- ^About the security content of macOS Sequoia 15.6.1 – Apple Support
- ^About the security content of iPadOS 17.7.10 – Apple Support
- ^NVD – CVE-2025-43300
- ^CVE-2025-43300 | Tenable®
- ^CVE-2025-43300 – Apple iOS, iPadOS, and macOS Out-of-Bounds Write Vulnerability – [Actively Exploited]
- ^Apple Patches CVE-2025-43300 Zero-Day in iOS, iPadOS, and macOS Exploited in Targeted Attacks
CVSS Breakdown Table
| Metric | Value | Description |
|---|---|---|
| Base Score | 8.8 | High severity enabling memory corruption and potential code execution when processing crafted image/DNG files |
| Attack Vector | Network | Triggered remotely via delivered image files (iMessage, Mail, AirDrop, web, etc.) |
| Attack Complexity | Low | Exploitation does not require special conditions |
| Privileges Required | None | No authentication or elevated privileges needed |
| User Interaction | Required | Exploit requires the device to process/preview the malicious image (per CVSS vector in your references) |
| Scope | UnChanged | Impact remains within the vulnerable Image I/O component on the device |
| Confidentiality Impact | High | Exploitation can expose sensitive data on the device |
| Integrity Impact | High | May allow unauthorized modification or code execution |
| Availability Impact | High | Can crash processes or lead to complete device compromise |