Summary
CVE-2025-9556 is a highimpact templateinjection flaw in Langchaingo caused by processing Jinja2style templates through the Gonja library v1.5.3. Gonja’s support for directives that include or extend templates (for example include / extends) can be abused by an attacker who controls prompt input to force the application to read files on the host (notably /etc/passwd).
Urgent Actions Required
- Update Langchaingo immediately to the version including the RenderTemplateFS fix (PR #1348).
- Disable parsing of Jinja2/Gonja syntax in user-controlled prompts until the patch is applied.
- Block or filter prompt inputs containing template directives ({% include %}, {% extends %}, {% from %}, {{ ... }}) via WAF or input validation.
- Run prompt-rendering services with minimal privileges and no access to sensitive files (e.g., /etc/passwd).
- Monitor logs for template syntax patterns in prompts to detect potential exploitation attempts.
Which Systems Are Vulnerable to CVE-2025-9556?
Technical Overview
- Vulnerability Type: Serverside template injection (SSTI) via template engine fileinclusion features
-
Affected Software/Versions:
- Langchaingo builds that use Gonja v1.5.3 (references identify Langchaingo 0.1.14 as affected).
- Gonja behavior in v1.5.3 (Jinja2style include/extends support) is the root cause.
- Attack Vector: Network (remote prompts / API inputs that are rendered)
- CVSS Score: 9.8
-
CVSS Vector: CVSS: 3.1
- Attack Vector: Network
- Attack complexity: Low
- Privileges required: None
- User interaction: None
- Scope: Unchanged
- Confidentiality impact: High
- Integrity impact: High
- Availability impact: High
- Patch Availability: Yes, available[1] [2]
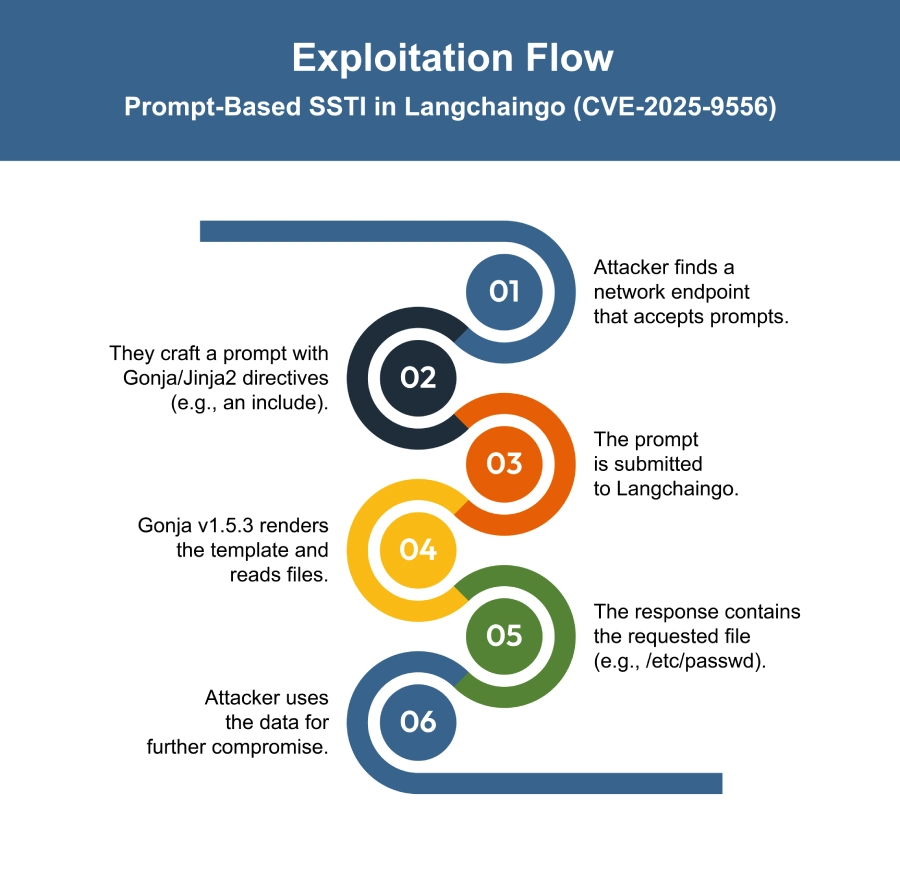
How Does the CVE-2025-9556 Exploit Work?
The attack typically follows these steps:
What Causes CVE-2025-9556?
Vulnerability Root Cause:
CVE-2025-9556 occurs because Langchaingo processes user-provided prompts using the Gonja templating engine (v1.5.3), which supports Jinja2 syntax including include and extends. These directives were not properly restricted, allowing attackers to craft prompts that force Gonja to read sensitive server files such as /etc/passwd. This creates a server-side template injection risk that can expose confidential data.
How Can You Mitigate CVE-2025-9556?
If immediate patching is delayed or not possible:
- Disable template parsing for untrusted prompts to prevent malicious input from being processed by Gonja.
- Block requests containing template-directive patterns such as {% include %}, {% extends %}, {% from %}, or {{ … }} using WAF or edge rules.
- Sanitize or allow list prompt inputs to only accept known-safe formats.
- Run prompt-rendering processes with minimal filesystem rights, restricting access to sensitive paths like /etc.
- Enable logging and detection to alert on prompts containing template directives or file paths.
- Isolate endpoints that accept prompts with network restrictions until the patch is applied.
- Update or configure Gonja usage to limit template access according to the vendor fix.
Which Assets and Systems Are at Risk?
Asset Types Affected:
- Applications using Langchaingo 0.1.14 or other versions that parse prompts with Gonja v1.5.3
- Systems where user input is processed through Langchaingo templates
Business-Critical Systems at Risk:
- Services relying on Langchaingo for dynamic content or prompt-based workflows
- Applications handling sensitive files or system information
Exposure Level:
- Internet-facing applications using Langchaingo without the patch
- Internal applications or services that process user-controlled prompts via Langchaingo
Will Patching CVE-2025-9556 Cause Downtime?
Patch application impact: Low. Updating Langchaingo to the patched version with RenderTemplateFS causes minimal downtime.
Temporary Mitigation: Restrict or sanitize Jinja2/Gonja prompts, but full protection requires the update.
How Can You Detect CVE-2025-9556 Exploitation?
Exploitation Signatures:
- Prompt or request text containing template markers: {%, %}, {{, }}.
- Template directives using inclusion/extension keywords: include, extends, from.
- Template text that references absolute filesystem paths (e.g., /etc/passwd).
MITRE ATT&CK Mapping:
- T1221[4]: Template engine misuse / template injection.
Indicators of Compromise (IOCs/IOAs):
- Logged prompt content containing {% include, {% extends, or {{ ... }} patterns.
- Responses from prompt-rendering endpoints that include plaintext matching system files (for example, /etc/passwd content).
- Network submissions of template-containing prompts to endpoints that accept or render prompts.
Behavioral Indicators:
- Prompt rendering returns filesystem content in ordinary responses.
Alerting Strategy:
- Priority: Critical
Alert triggers:
- Any incoming prompt containing template tokens together with include, extends, or from.
- Any response from a prompt-rendering endpoint that contains recognizable system-file content (for example, passwd format, private-key headers, or DB config snippets).
Immediate actions on alert:
- Capture and preserve the full prompt and the rendered response for forensic review.
- Block or throttle the source IP and associated sessions pending investigation.
- Verify whether the affected host is running the vulnerable template rendering stack (Langchaingo using Gonja v1.5.3 / Langchaingo 0.1.14) and prioritize applying the vendor fix.
Remediation & Response
Incident Response Considerations:
- Isolate any affected applications to prevent further exploitation.
- Collect and preserve prompt logs and rendered outputs for forensic investigation.
- Check whether sensitive files (e.g., /etc/passwd) or internal data were exposed.
- After patching, validate that secure template rendering is active and continue monitoring for template injection attempts.
Where Can I Find More Information on CVE-2025-9556?
- ^Langchaingo supports the use of jinja2 syntax when… · CVE-2025-9556 · GitHub Advisory Database · GitHub
- ^prompts: Prompt template improvements and docs expansion by tmc · Pull Request #1348 · tmc/langchaingo · GitHub
- ^CVE-2025-9556 : Server Side Template Injection Vulnerability in Langchaingo by TMC
- ^Template Injection, Technique T1221 – Enterprise | MITRE ATT&CK®
CVSS Breakdown Table
| Metric | Value | Description |
|---|---|---|
| Base Score | 9.8 | Critical, easily exploitable with severe impact on data and system security |
| Attack Vector | Network | Exploitable remotely via networked prompt inputs |
| Attack Complexity | Low | No special conditions required |
| Privileges Required | None | No authentication or elevated rights needed |
| User Interaction | None | Exploitation does not require user action |
| Scope | UnChanged | Impact remains within the vulnerable component |
| Confidentiality Impact | High | Arbitrary file read (e.g., /etc/passwd) - sensitive data exposure |
| Integrity Impact | High | Exploit allows modification or misuse of data |
| Availability Impact | High | Successful attacks may disrupt service or block access |