Fidelis Network® Detection and Response
for your Network
Fidelis Network® Detection and Response
9X Faster
Fidelis Security® has been Protecting Leading Enterprises Worldwide for over 20 years
Cellphone manufacturer
Largest Defense Contractor
Convenience Store Chain
Pharmacy Chain
Mobile Service Provider
Pharmaceutical Company

Network Detection and Response
Network Detection and Response (NDR) is a crucial cybersecurity solution aimed at swiftly identifying and responding to threats within network environments. NDR security solutions usually comprises of:
- Real-time Monitoring
- Threat Detection
- Rapid Response Capabilities
- Proactive Defence Strategy

Fidelis Network®: A Unified Network Security Solution
Fidelis Network® is an NDR platform that offers full and deep internal visibility across all ports and protocols, with network traffic analysis and network behaviour anomaly detection, which monitors for potential security threats, and signs of malicious activity.
For automation of responses, Fidelis Network® is equipped with technologies like:
- Network Data Loss Prevention
- Sandboxing
- Deep Session Inspection
- Advance Cyber Terrain Mapping
What Sets Fidelis NDR Apart?
#1 solution for visibility and inspection of data in motion
Full Visibility
Fidelis Network®, our NDR security solution, provides unmatched visibility of your cyber terrain by coupling deep visibility with risk assessment to profile, classify, and identify risky assets and users.
Our customers detect post-breach attacks 9x faster
Faster Response to Threats
Fidelis Network® (NDR solution) catches risks other tools don’t. It is equipped with network behaviour anomaly detection, data loss prevention technology and active threat detection.
Fidelis has identified 6.7M high severity malware threats to this date
Highly Efficient Threat Hunting
Finding threats in rapidly growing and changing environments requires automation and intelligence. Fidelis Network® supplies both. Working along with Fidelis Decryption®, Fidelis achieves comprehensive network security by giving one both the content and context of threats in one place.
Threat Protection offered by Fidelis Network® Detection and Response
Data Theft
One of the most technical ways attackers use to steal data is data exfiltration. Fidelis Network® unpacks and extract deeply embedded files to detect data exfiltration, with patented Deep Session Inspection.
Lateral Movement in Network
Fidelis Network® allows you to Understand what’s moving across your network, how it’s moving, and who is seeing it with the help of automated risk-aware terrain mapping, and patented traffic analysis tools
Malware Threat
Fidelis Network® gives you a clear picture of bi-directional encrypted traffic, with content and context. It also allows you to decrypt for deeper analysis to detect malware on the wire.
There’s a Reason the Most Important Data on Earth is protected by Fidelis
of the 6 US Military Branches Defended
of the 10 Largest US Government Agencies Protected
Year-to-Date High Severity Malware Threats Identified
Year-to-Date Critical Vulnerability Exploitations Attempts Detected
There’s a Reason the Most Important Data on Earth is protected by Fidelis
of the 6 US Military Branches Defended
of the 10 Largest US Government Agencies Protected
Year-to-Date High Severity Malware Threats Identified
Year-to-Date Critical Vulnerability Exploitations Attempts Detected
Decode Your Network's Secret
Know your Environment better than Attackers!
With automated risk-aware terrain mapping, and patented traffic analysis tools, the Fidelis NDR security platform offers full and deep internal visibility across ports and protocols, and monitors network traffic for anomalous behavior, potential security threats, and signs of malicious activity.
Why is Fidelis winning against its competitors?
Our customers detect post-breach attacks over 9x faster.
Related Resources

The Latest Trend in Network Cybersecurity: NDR
Explore Network Detection and Response (NDR) insights in this whitepaper. Learn about prevention, automated investigation, incident analysis, and retrospective analysis.
Network DLP Solution: Key Features & Considerations
Navigate the network DLP challenge effectively. Learn about key features for data security & considerations for the best Network DLP
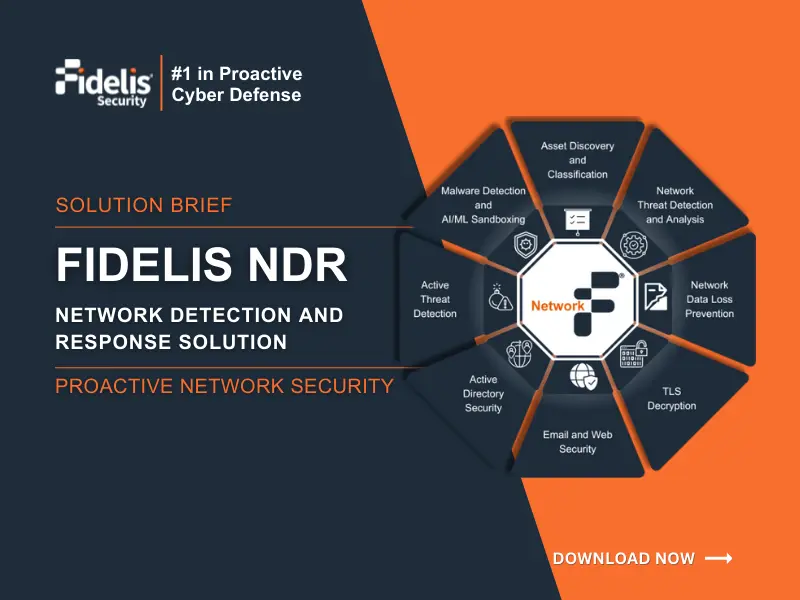
Proactive Network Cyber Defense for Hybrid Environment: Fidelis NDR
Discover how Fidelis Network offers proactive cybersecurity for hybrid work environments. Detect threats faster, improve visibility, and eliminate alert fatigue.

The Latest Trend in Network Cybersecurity: NDR
Explore Network Detection and Response (NDR) insights in this whitepaper. Learn about prevention, automated investigation, incident analysis, and retrospective analysis.
Network DLP Solution: Key Features & Considerations
Navigate the network DLP challenge effectively. Learn about key features for data security & considerations for the best Network DLP
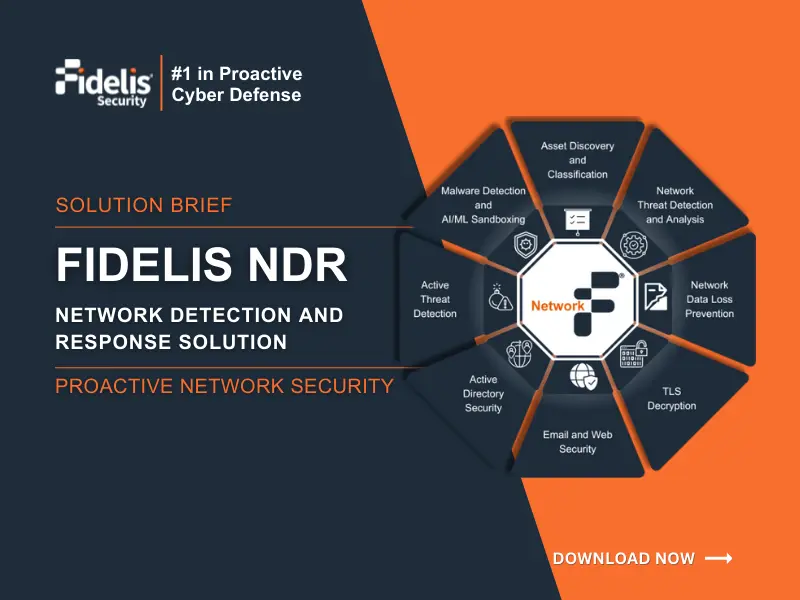
Proactive Network Cyber Defense for Hybrid Environment: Fidelis NDR
Discover how Fidelis Network offers proactive cybersecurity for hybrid work environments. Detect threats faster, improve visibility, and eliminate alert fatigue.