Summary
CVE-2025-6218 is a critical directory traversal flaw in WinRAR (v7.11 and earlier) that lets attackers execute code by tricking users into opening malicious archive files. Exploitable via phishing or malvertising, it’s fixed in v7.12 Beta 1. Update now and avoid untrusted archives to reduce risk.
Urgent Actions Required
- Update WinRAR to version 7.12 or later immediately.
- Avoid opening archive files from unknown or untrusted sources.
- Use up-to-date antivirus and endpoint protection tools.
- Scan archive contents before extraction.
- Conduct user awareness training on archive-based threats.
Which Systems Are Vulnerable to CVE-2025-6218?
Technical Overview
- Vulnerability Type: Directory Traversal Leading to Remote Code Execution (RCE)
- Affected Software/Versions:
- WinRAR for Windows versions 7.11 and earlier
- RAR, UnRAR, UnRAR.dll, and Portable UnRAR (Windows only)
(Unix and Android versions are not affected)
- Attack Vector: Local (User-assisted - e.g., opening a malicious archive)
- CVSS Score: 7.8
- Exploitability Score: 1.8
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Patch Availability: Yes — fixed in WinRAR 7.12 Beta 1 and later
WinRAR Latest News
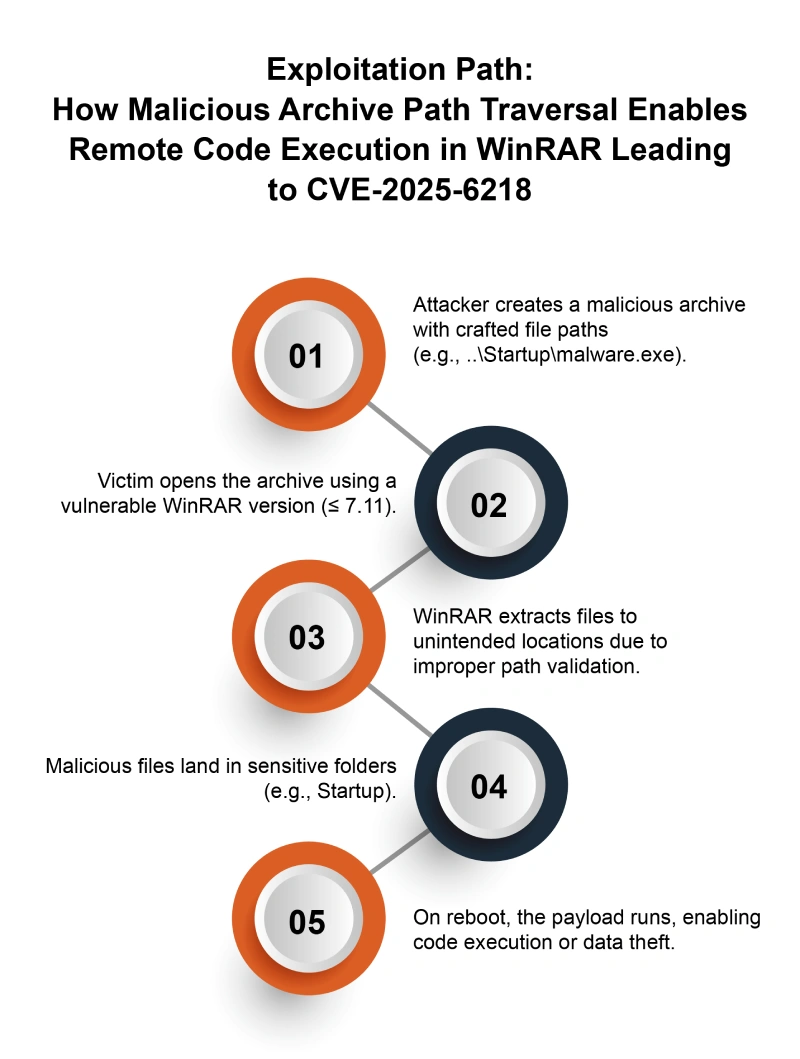
How Does the CVE-2025-6218 Exploit Work?
The attack typically follows these steps:
What Causes CVE-2025-6218?
Vulnerability Root Cause:
This vulnerability is caused by improper path validation in WinRAR. Malicious archives with crafted paths (like ../) can extract files outside the intended folder, such as Windows startup. This allows remote code execution when opened, risking full system compromise.
How Can You Mitigate CVE-2025-6218?
If immediate patching is delayed or not possible:
- Don’t open archive files from unknown sources.
- Use a sandbox or isolated setup for suspicious archives.
- Use EDR solutions and antivirus software that detect archive-based threats.
- Watch for unexpected changes in sensitive folders (like startup).
- Limit write access to important system directories.
- Train users to avoid unknown or unsolicited compressed files.
Which Assets and Systems Are at Risk?
Asset Types Affected:
- Desktop Applications – Specifically, RARLAB WinRAR for Windows (versions 7.11 and earlier)
- File Extraction Utilities – Any systems using WinRAR, UnRAR, or UnRAR.dll
- Legacy Software Installations – Systems with outdated versions of WinRAR commonly used in enterprise and consumer environments
Business-Critical Systems at Risk:
- Workstations with Startup Scripts – Malicious payloads can be silently dropped into auto-run directories
- Shared Office PCs – Especially in environments lacking strict user access controls
- Systems with Access to Sensitive Data – Files extracted via vulnerable WinRAR versions could exfiltrate credentials, browser cookies, or install remote access tools
- Endpoint Systems in Large Enterprises – Used by employees for decompressing archives, potentially exposing the wider network
Exposure Level:
- Internet-facing endpoints – If users download and open malicious archives from phishing emails or untrusted websites
- Internal workstations – Especially if legacy WinRAR versions are widely installed and patching is inconsistent
- Remote workers or BYOD devices – With outdated WinRAR versions, lacking centralized update enforcement
Will Patching CVE-2025-6218 Cause Downtime?
Patch application impact: Low. Update to WinRAR version 7.12 or later to fix the issue. Since WinRAR doesn’t auto-update, you’ll need to install it manually. Most users won’t face issues, but organizations should check for compatibility with automated tools.
Mitigation (if immediate patching is not possible): You can reduce risk by avoiding opening files from unknown sources, running WinRAR in a restricted environment, using antivirus software, and blocking suspicious programs from auto-starting. But these steps don’t fully fix the problem—until you update WinRAR, your system can still be hacked using specially crafted files.
How Can You Detect CVE-2025-6218 Exploitation?
Exploitation Signatures:
Look for archive files containing file paths with suspicious traversal patterns like ../ or encoded variants that attempt to escape intended directories.
MITRE ATT&CK Mapping:
- T1071[4] – Application Layer Protocol (exploitation via crafted archive files)
- T1204[5] – User Execution (requires user to open malicious archive)
- T1068[6] – Exploitation for Privilege Escalation (potential post-exploit action)
Indicators of Compromise (IOCs/IOAs):
- Archive files with crafted file paths containing directory traversal sequences (../)
- Unexpected files appearing outside of extraction directories
- Execution of files dropped via extracted archives without user consent
Behavioral Indicators:
- Unexpected code execution or new files appearing after archive extraction
- Auto-run or startup folder modifications linked to extracted archives
- Unusual process activity launched by WinRAR or related processes following archive extraction
Alerting Strategy:
- Priority: High
- Trigger alerts for:
- Extraction or opening of archives containing directory traversal paths
- Execution of newly extracted files in auto-run or startup locations
- Detection of unusual WinRAR behavior or process launches after archive handling
Remediation & Response
Patch/Upgrade Instructions:
- WinRAR Patch Advisory:
WinRAR Latest News
Remediation Timeline:
- Immediate (0–2 hrs): Enforce safe extraction policies and sandbox WinRAR usage.
- Within 24 hrs: Update all WinRAR instances to version 7.12 or newer.
- Within 48 hrs: Verify no vulnerable versions remain on critical systems.
Rollback Plan::
- If upgrading causes issues, revert to the previous stable WinRAR version while maintaining strict extraction policies and sandboxing until a full patch can be applied.
- Document rollback steps clearly with version details and responsible personnel.
Incident Response Considerations:
- Isolate affected systems to prevent further exploitation.
- Gather forensic data like extraction logs and file changes.
- Check for signs of code execution, unauthorized access, or malware from bad archives.
- After updating, improve monitoring of archive activity and confirm the fix works.
Where Can I Find More Information on CVE-2025-6218?
CVSS Breakdown Table
| Metric | Value | Description |
|---|---|---|
| Base Score | 7.8 | High severity vulnerability with significant impact and exploitability |
| Attack Vector | Local | Exploitation requires local user interaction to open a malicious archive |
| Attack Complexity | Low | Exploitation does not require special conditions beyond opening the crafted archive |
| Privileges Required | None | No elevated privileges needed to trigger the vulnerability |
| User Interaction | Required | User must open the maliciously crafted archive file |
| Scope | Unchanged | Impact is limited to the affected system without extending beyond |
| Confidentiality Impact | High | Successful exploitation can lead to unauthorized data access or disclosure |
| Integrity Impact | High | Exploit can allow arbitrary code execution and unauthorized modification |
| Availability Impact | Low to None | Exploitation could result in system compromise or denial of service |



