Copyright © Fidelis Security. All rights reserved.
-
Privacy PolicyPrivacy Policy
-
Terms of ServiceTerms of Service
-
Trust CenterTrust Center
-
SecuritySecurity
Explore Proactive Cybersecurity Solution Offered by Us!
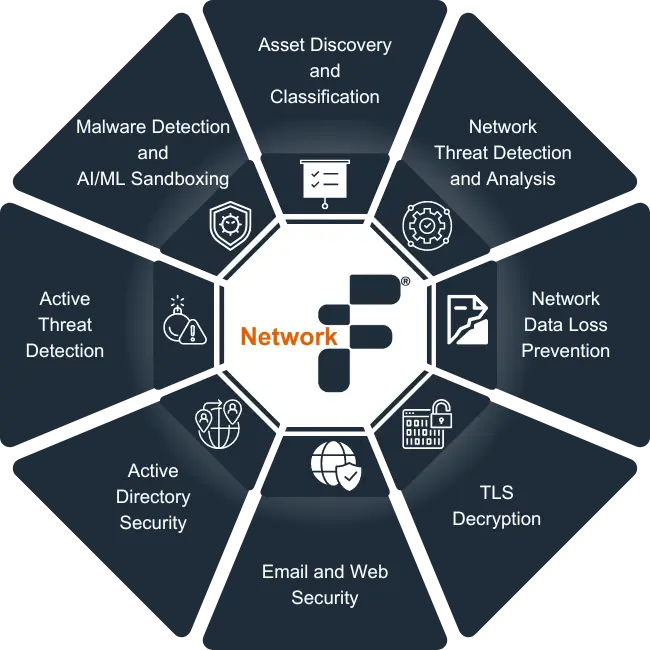
Enhance your network security 9X faster with our advanced Network Detection & Response (NDR) solution, guarding against evolving threats and breaches.
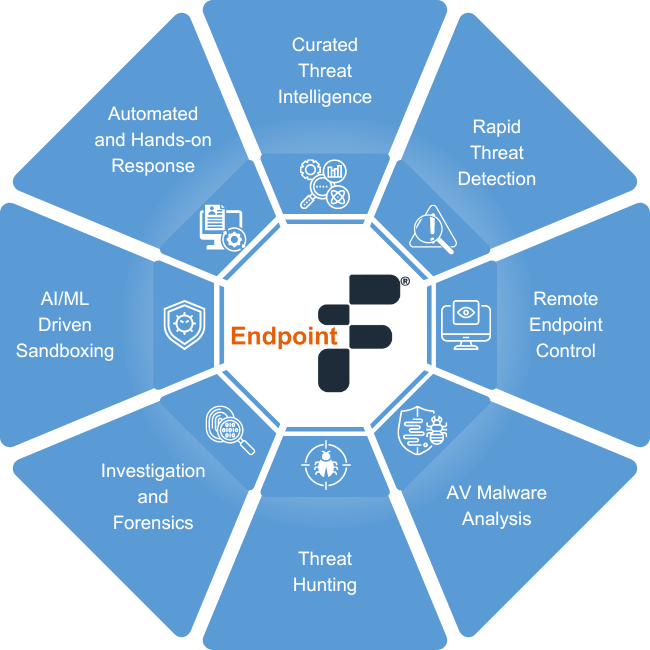
Elevate your cybersecurity defenses with state-of-the-art Endpoint Detection and Response (EDR) solution. Safeguard your endpoints with robust endpoint security measures.
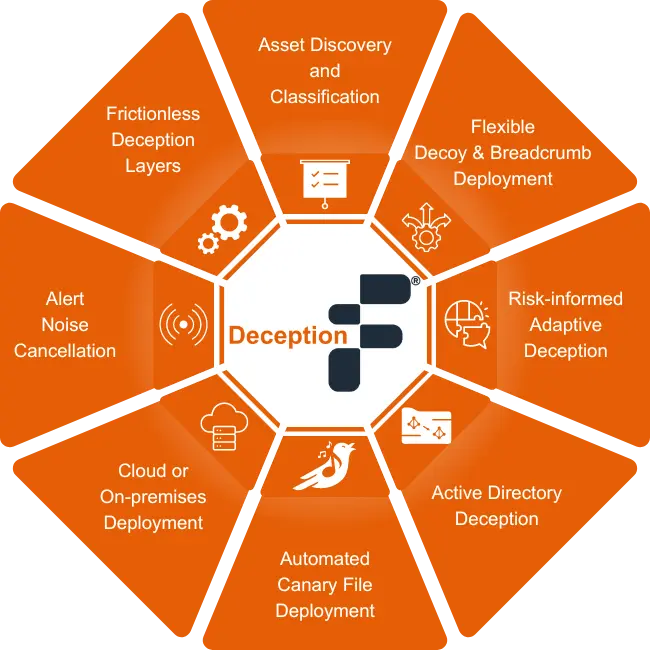
Discover cutting-edge deception technology solutions for enhanced cybersecurity. Explore our product range designed to outsmart cyber threats.
Join our newsletter to stay up to date on features and releases.