
Multi-layered Defense: Enhancing Security with Fidelis Active Directory Intercept™
Discover the power of Fidelis Active Directory Intercept for a robust multi-layered defense. Safeguard your AD infrastructure against evolving cyber threats…
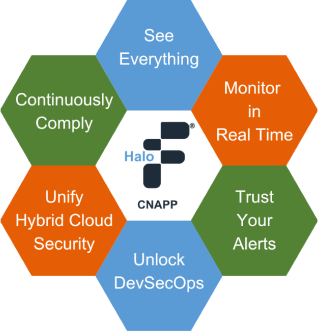

Discover the power of Fidelis Active Directory Intercept for a robust multi-layered defense. Safeguard your AD infrastructure against evolving cyber threats…

On May 31, 2023 Progress Software disclosed a SQL injection vulnerability (CVE-2023-34362) in the MOVEit Transfer that could lead to escalated privileges
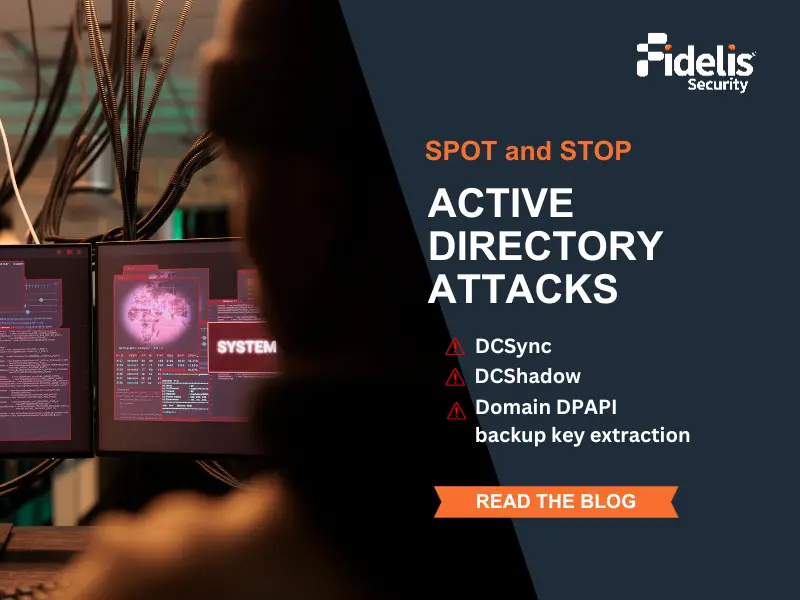
In the previous blog, we described how to catch attackers targeting Active Directory (AD) in the reconnaissance stage, which is

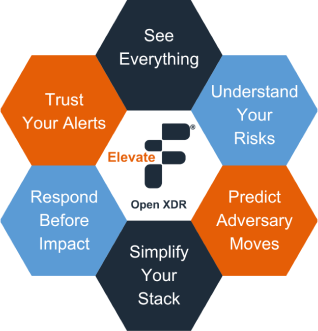
Is your organization’s security strategy prepared to face modern cyber threats? Cyber threats are evolving at an unprecedented pace, demanding

Discover the power of Fidelis Active Directory Intercept for a robust multi-layered defense. Safeguard your AD infrastructure against evolving cyber threats…

On May 31, 2023 Progress Software disclosed a SQL injection vulnerability (CVE-2023-34362) in the MOVEit Transfer that could lead to escalated privileges
In the previous blog, we described how to catch attackers targeting Active Directory (AD) in the reconnaissance stage, which is

Is your organization’s security strategy prepared to face modern cyber threats? Cyber threats are evolving at an unprecedented pace, demanding
Join our newsletter to stay up to date on features and releases.